[ad_1]
Twitter’s new proprietor, Elon Musk, is feverishly selling his “Twitter Files”: chosen inside communications from the corporate, laboriously tweeted out by sympathetic amanuenses. However Musk’s apparent conviction that he has launched some partisan kraken is mistaken — removed from conspiracy or systemic abuse, the recordsdata are a worthwhile peek behind the scenes of moderation at scale, hinting on the Sisyphean labors undertaken by each social media platform.
For a decade, corporations like Twitter, YouTube, and Fb have carried out an elaborate dance to maintain the small print of their moderation processes equally out of attain of unhealthy actors, regulators, and the press.
To disclose an excessive amount of can be to show the processes to abuse by spammers and scammers (who certainly reap the benefits of each leaked or revealed element), whereas to disclose too little results in damaging experiences and rumors as they lose management over the narrative. In the meantime, they have to be able to justify and doc their strategies or threat censure and fines from authorities our bodies.
The result’s that whereas everybody is aware of a little about how precisely these corporations examine, filter, and organize the content material posted on their platforms, it’s simply sufficient to make sure that what we’re seeing is barely the tip of the iceberg.
Generally there are exposés of the strategies we suspected — by-the-hour contractors clicking by way of violent and sexual imagery, an abhorrent but apparently necessary industry. Generally the businesses overplay their arms, like repeated claims of how AI is revolutionizing moderation and subsequent experiences that AI methods for this objective are inscrutable and unreliable.
What virtually by no means occurs — typically corporations don’t do that except they’re pressured to — is that the precise instruments and processes of content material moderation at scale are uncovered with no filter. And that’s what Musk has executed, maybe to his personal peril, however certainly to the good curiosity of anybody who ever questioned what moderators really do, say, and click on as they make selections which will have an effect on hundreds of thousands.
Pay no consideration to the sincere, advanced dialog behind the scenes
The e-mail chains, Slack conversations, and screenshots (or relatively photographs of screens) launched during the last week present a glimpse at this necessary and poorly understood course of. What we see is a little bit of the uncooked materials, which isn’t the partisan illuminati some anticipated — although it’s clear, by its extremely selective presentation, that that is what we are supposed to understand.
Removed from it: the folks concerned are by turns cautious and assured, sensible and philosophical, outspoken and accommodating, exhibiting that the selection to restrict or ban isn’t made arbitrarily however in response to an evolving consensus of opposing viewpoints.
(Replace: Moments after I posted this, a new thread started that’s extra of the identical — earnest discussions of advanced points in coordination with consultants, regulation enforcement, and others.)
Main as much as the selection to briefly limit the Hunter Biden laptop computer story — in all probability at this level essentially the most contentious moderation choice of the previous couple of years, behind banning Trump — there may be neither the partisanship nor conspiracy insinuated by the bombshell packaging of the paperwork.
As a substitute we discover severe, considerate folks making an attempt to reconcile conflicting and insufficient definitions and insurance policies: What constitutes “hacked” supplies? How assured are we on this or that evaluation? What’s a proportionate response? How ought to we talk it, to whom, and when? What are the implications if we do, if we don’t restrict? What precedents will we set or break?
The solutions to those questions are in no way apparent and are the form of factor normally hashed out over months of analysis and dialogue, and even in courtroom (authorized precedents have an effect on authorized language and repercussions). And so they wanted to be made quick, earlier than the scenario acquired uncontrolled someway. Dissent from inside and with out (from a U.S. Consultant, no much less — mockingly, doxxed within the thread together with Jack Dorsey in violation of the selfsame coverage) was thought of and truthfully built-in.
“That is an rising scenario the place the information stay unclear,” stated former Belief and Security chief Yoel Roth. “We’re erring on the facet of together with a warning and stopping this content material from being amplified.”
Some query the choice. Some query the information as they’ve been offered. Others say it’s not supported by their studying of the coverage. One says they should make the advert hoc foundation and extent of the motion very clear since it’ll clearly be scrutinized as a partisan one. Deputy Basic Counsel Jim Baker requires extra data however says warning is warranted. There’s no clear precedent; the information are at this level absent or unverified; among the materials is plainly nonconsensual nude imagery.
“I imagine Twitter itself ought to curtail what it recommends or places in trending information, and your coverage towards QAnon teams is all good,” concedes Rep. Ro Khanna, whereas additionally arguing the motion in query is a step too far. “It’s a tough steadiness.”
Neither the general public nor the press have been privy to those conversations, and the reality is we’re as curious, and largely as at nighttime, as our readers. It will be incorrect to name the revealed supplies a whole and even correct illustration of the entire course of (they’re blatantly, if ineffectively, picked and chosen to suit a story), however even equivalent to they’re we’re extra knowledgeable than we had been earlier than.
Instruments of the commerce
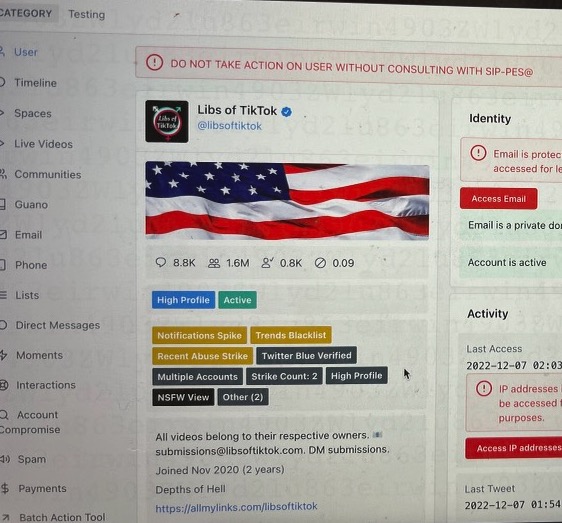
Much more straight revealing was the following thread, which carried screenshots of the particular moderation tooling utilized by Twitter staff. Whereas the thread disingenuously makes an attempt to equate the usage of these instruments with shadow banning, the screenshots don’t present nefarious exercise, nor do they should to be able to be attention-grabbing.
Picture Credit: Twitter
Quite the opposite, what’s proven is compelling for the very cause that it’s so prosaic, so blandly systematic. Listed below are the assorted methods all social media corporations have defined again and again that they use, however whereas earlier than we had it couched in PR’s cheery diplomatic cant, now it’s offered with out remark: “Developments Blacklist,” “Excessive Profile,” “DO NOT TAKE ACTION” and the remaining.
In the meantime, Yoel Roth explains that the actions and insurance policies have to be higher aligned, that extra analysis is required, that plans are underway to enhance:
The speculation underlying a lot of what we’ve carried out is that if publicity to, e.g., misinformation straight causes hurt, we must always use remediations that scale back publicity, and limiting the unfold/virality of content material is an efficient manner to try this… we’re going to want to make a extra strong case to get this into our repertoire of coverage remediations — particularly for different coverage domains.
Once more the content material belies the context it’s offered in: these are hardly the deliberations of a secret liberal cabal lashing out at its ideological enemies with a ban hammer. It’s an enterprise-grade dashboard such as you would possibly see for lead monitoring, logistics, or accounts, being mentioned and iterated upon by sober-minded individuals working inside sensible limitations and aiming to fulfill a number of stakeholders.
Accurately: Twitter has, like its fellow social media platforms, been working for years to make the method of moderation environment friendly and systematic sufficient to perform at scale. Not simply so the platform isn’t overrun with bots and spam, however to be able to adjust to authorized frameworks like FTC orders and the GDPR. (Of which the “intensive, unfiltered entry” outsiders got to the pictured instrument could nicely represent a breach. The related authorities instructed TechCrunch they are “engaging” with Twitter on the matter.)
A handful of staff making arbitrary selections with no rubric or oversight is not any technique to average successfully or meet such authorized necessities; neither (because the resignation of a number of on Twitter’s Belief & Security Council at present testifies) is automation. You want a big community of individuals cooperating and dealing in response to a standardized system, with clear boundaries and escalation procedures. And that’s definitely what appears to be proven by the screenshots Musk has prompted to be revealed.
What isn’t proven by the paperwork is any form of systematic bias, which Musk’s stand-ins insinuate however don’t fairly handle to substantiate. However whether or not or not it suits into the narrative they need it to, what’s being revealed is of curiosity to anybody who thinks these corporations should be extra forthcoming about their insurance policies. That’s a win for transparency, even when Musk’s opaque method accomplishes it kind of accidentally.
[ad_2]
Source link









